Thanks for replying master.
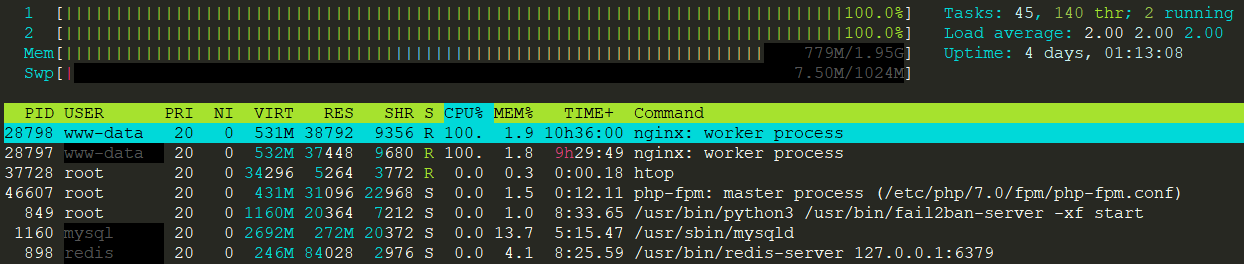
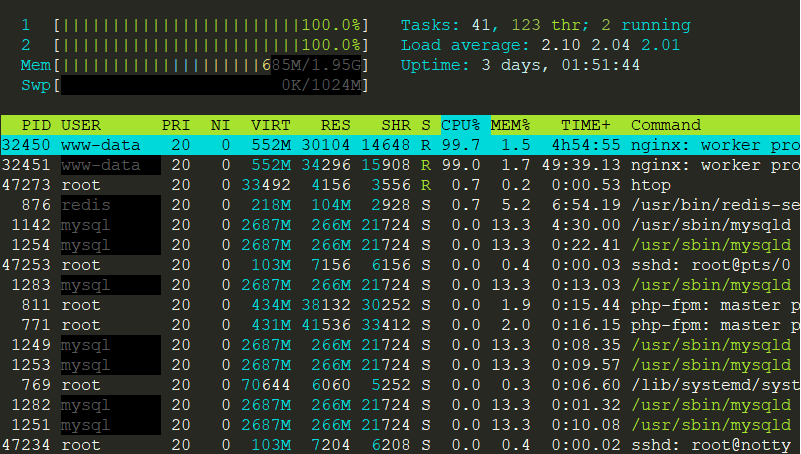
It has been almost 18 Hours yet the Nginx wasn’t failed but just now it happened again. When I checked through htop Command I found that Nginx Worker Process with PID 32450 is consuming 100% CPU as shown in the following image:
Then, I checked nginx error.log but it was empty. Later, I opened the particular site’s error log and found the following entry there:
2018/10/30 14:34:06 [error] 32450#32450: *470 access forbidden by rule, client: 219.91.191.146, server: examweb.in, request: "HEAD /https://www.examweb.in/ HTTP/1.1", host: "www.examweb.in"
2018/10/30 15:20:44 [error] 32450#32450: *1602 access forbidden by rule, client: 88.198.69.233, server: examweb.in, request: "GET /%E0%A4%A8%E0%A5%8B%E0%A4%9F%E0%A4%AC%E0%A4%82%E0%A4%A6%E0%A5%80-%E0%A4%AA%E0%A4%B0-%E0%A4%B2%E0%A5%87%E0%A4%96-%E0%A4%A8%25 HTTP/1.1", host: "www.examweb.in"
2018/10/30 17:23:43 [crit] 32450#32450: *5012 SSL_do_handshake() failed (SSL: error:1417D0A0:SSL routines:tls_process_client_hello:length too short) while SSL handshaking, client: 108.178.16.154, server: 0.0.0.0:443
One More Website’s Error Log
2018/10/30 21:17:42 [error] 32450#32450: *12453 access forbidden by rule, client: 115.235.172.205, server: ishaweb.in, request: "GET /motilal-nehru-sports-school-rai-admission... HTTP/1.1", host: "www.ishaweb.in"
2018/10/30 22:08:58 [error] 32450#32450: *13748 access forbidden by rule, client: 35.237.3.156, server: ishaweb.in, request: "GET /wp-json/wp/v2/posts/10725,%22href%22:%22https:%5C/%5C/www.ishaweb.in%5C/wp-json%5C/wp%5C/v2%5C/posts%5C/6627%5C/revisions%5C/10725%22%7D],%22wp:attachment%22:[%7B%22href%22:%22https:%5C/%5C/www.ishaweb.in%5C/wp-json%5C/wp%5C/v2%5C/media?parent=6627%22%7D],%22wp:term%22:[%7B%22taxonomy%22:%22category%22,%22embeddable%22:true,%22href%22:%22https:%5C/%5C/www.ishaweb.in%5C/wp-json%5C/wp%5C/v2%5C/categories?post=6627%22%7D,%7B%22taxonomy%22:%22post_tag%22,%22embeddable%22:true,%22href%22:%22https:%5C/%5C/www.ishaweb.in%5C/wp-json%5C/wp%5C/v2%5C/tags?post=6627%22%7D],%22curies%22:[%7B%22name%22:%22wp%22,%22href%22:%22https:%5C/%5C/api.w.org%5C/%7Brel%7D%22,%22templated%22:true%7D]%7D%7D,%7B%22id%22:6848 HTTP/1.1", host: "www.ishaweb.in"
Here is the output of commands you asked for:
nginx/1.15.5 (VirtuBox Nginx-ee)
AND
Active connections: 28
server accepts handled requests
19948 19948 27961
Reading: 0 Writing: 2 Waiting: 26